Microsoft 365 ISO:27001 Compliance Management Using AdminDroid
The ISO:27001 compliance requires all IT organizations to protect their information security management systems for securing data. Every organization can develop certain rules based on their requirements and compare them with these ISO:27001 Annex A controls to ensure that they are following better controls to secure their organization.
If you are seeking an authentic tool to generate cutting-edge compliance reports for ISO audits, undeniably, it’s none other than AdminDroid.
Being an ISO compliance reporting tool for Microsoft 365, AdminDroid provides you end-to-end visibility into your organization with a big picture to protect your information system and comply with ISO:27001.

What is ISO:27001?
The members & authorities of the International Organization for Standardization (ISO) and the International Electrochemical Commission (IEC) developed certain standards and rules for protecting Information Security Management Systems (ISMS). The standards are now revised in 2022 and come up with 93 controls. In the recent update, six new controls are added in ISO: 27001 Annex A table to secure your information from emerging threats.
These security controls can be used by both internal and external parties to audit the organization’s ability to meet information security requirements. It helps to secure your organization’s confidential data from intruders.
Note: Don’t get confused with Annex A controls which are derived from ISO:27002. It is not a separate standard, but it is a supporting standard for ISO:27001 and guides on how to implement the security controls properly in the organization to achieve ISO:27001 audit.
Why does Microsoft 365 Environment need to be ISO:27001 Compliant?
ISO will help manage the security of confidential data such as employee records, customer data, financial details, and more. In Microsoft 365, such sensitive records are scattered and stored for various purposes. Thus, you must comply with ISO:27001 controls to secure your Microsoft 365 environment and avoid data breaches.
Does Microsoft’s ISO:27001 Certification Exclude Us from Individual Compliance Audits?
Verifying your organization's security controls with ISO:27001 standards is required for the following reasons.
- Though Microsoft provides necessary security configurations and policies, some of them are applied by default, and some need to be manually configured based on the organization's needs.
- Also, Microsoft requires customers to opt for various license plans to utilize the full potential of compliance controls. So, customers may rely on any third-party tools to optimize their budget.
Thus, auditing every bit of security controls configured in your organization is prominent to comply with the ISO:27001 controls.
Shortcomings in Microsoft 365 Compliance Management with Native Tools
Besides all the advantages of Microsoft 365, it falls short when it comes to the following concerns:
Long Retention of Audit Data Requires Budget Boost
For compliance requirements, you need to retain the audit log for a long period. But Microsoft 365 audit logs let you retain records for up to 10 years with an Audit Premium license which increases your budget.
Limited Reports to Comply with Compliance Standards
In Microsoft 365, you will have only a limited number of reports required for monitoring and securing your information systems.
Monitoring Audit Log Becomes Challenging
Audit records return massive data based on your search query. Spotting specific activity and finding details becomes a real trouble for admins.
Breaking the Compliance Barrier: How AdminDroid Enhances your ISO:27001 Audit?
Wave goodbye to data retention woes and step up your ISO:27001 compliance with tailored Microsoft 365 reports from AdminDroid.
AdminDroid reports are absolutely a treasure house for monitoring compliance reports on time for your ISO audit process. Being customizable and providing in-depth details with AI-generated charts make our reports the top choice for all your compliance desires. You don’t need to navigate multiple portals to find specific reports. Get all the required reports in hand within seconds with our ISO report bundle.
Also, avoid excessive privileges to your compliance reports in a few clicks with AdminDroid’s granular delegation. It lets you delegate your compliance admin to access only compliance-related reports in the AdminDroid portal.
ISO requires organizations to retain audit records for 3 years. Don’t worry about a budget hike when AdminDroid is with you! Grab AdminDroid ISO compliance management software and retain your Microsoft 365 audit logs infinitely. To make your ISO compliance smoother, we have mapped our compliance reports with ISO:27001 Annex A standards.
Note: AdminDroid provides compliance reports for fulfilling both ISO:27001 2013 and ISO:27001 2022 versions.
From Implementation to Management: Fulfill ISO-27001 Compliance with AdminDroid
If you rely on Microsoft 365, then you should make sure that your information system complies with ISO:27001 controls. These controls can be used by your internal audit team and external auditor to verify your organization’s information security capabilities.
We have compiled two mappings from which you can implement and manage ISO:27001 controls in your Microsoft 365 environment efficiently.

Stay Ahead of the Curve with AdminDroid’s ISO Readiness Solutions
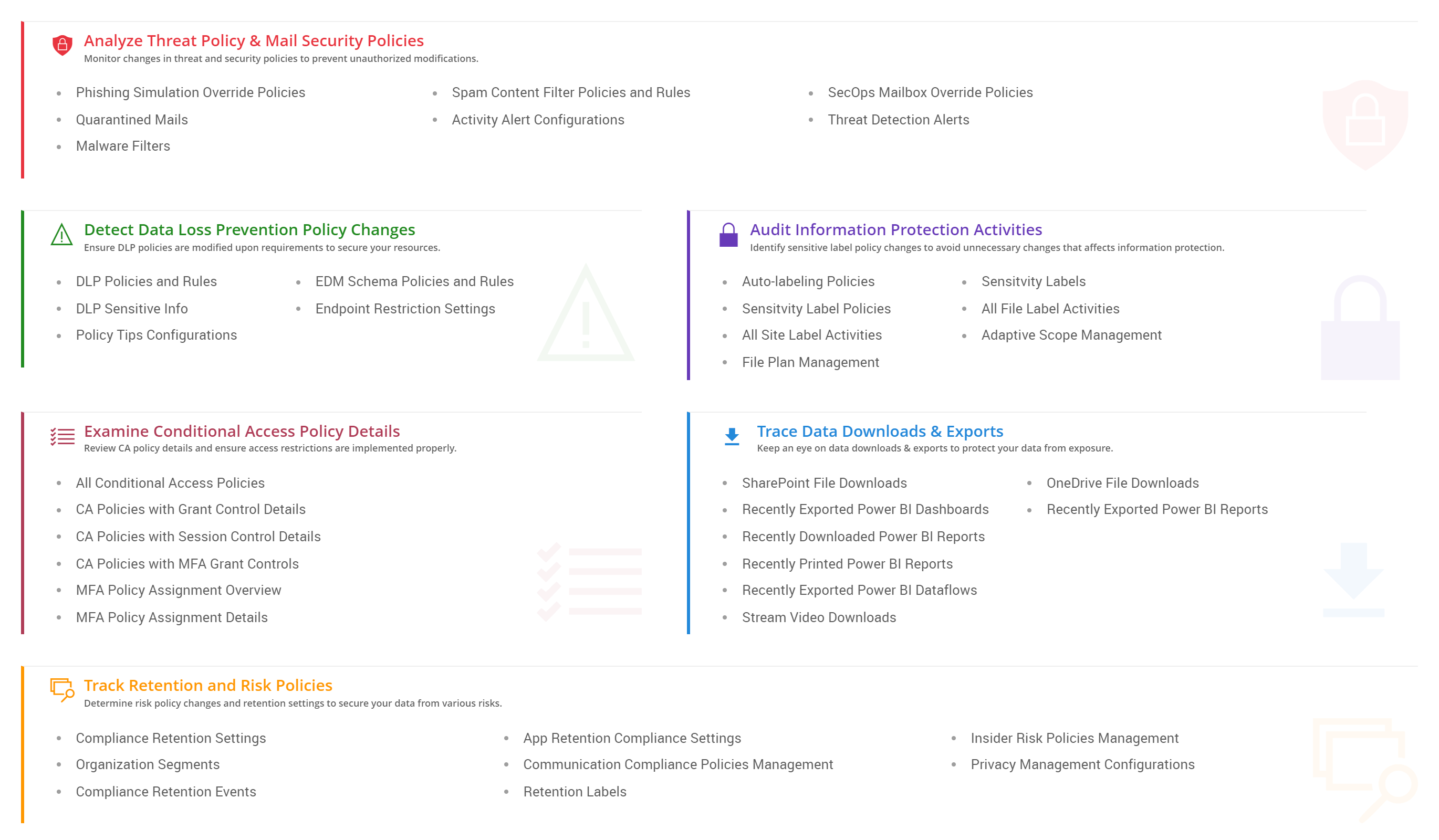
Detect crucial security policy changes and track data downloads & exports.
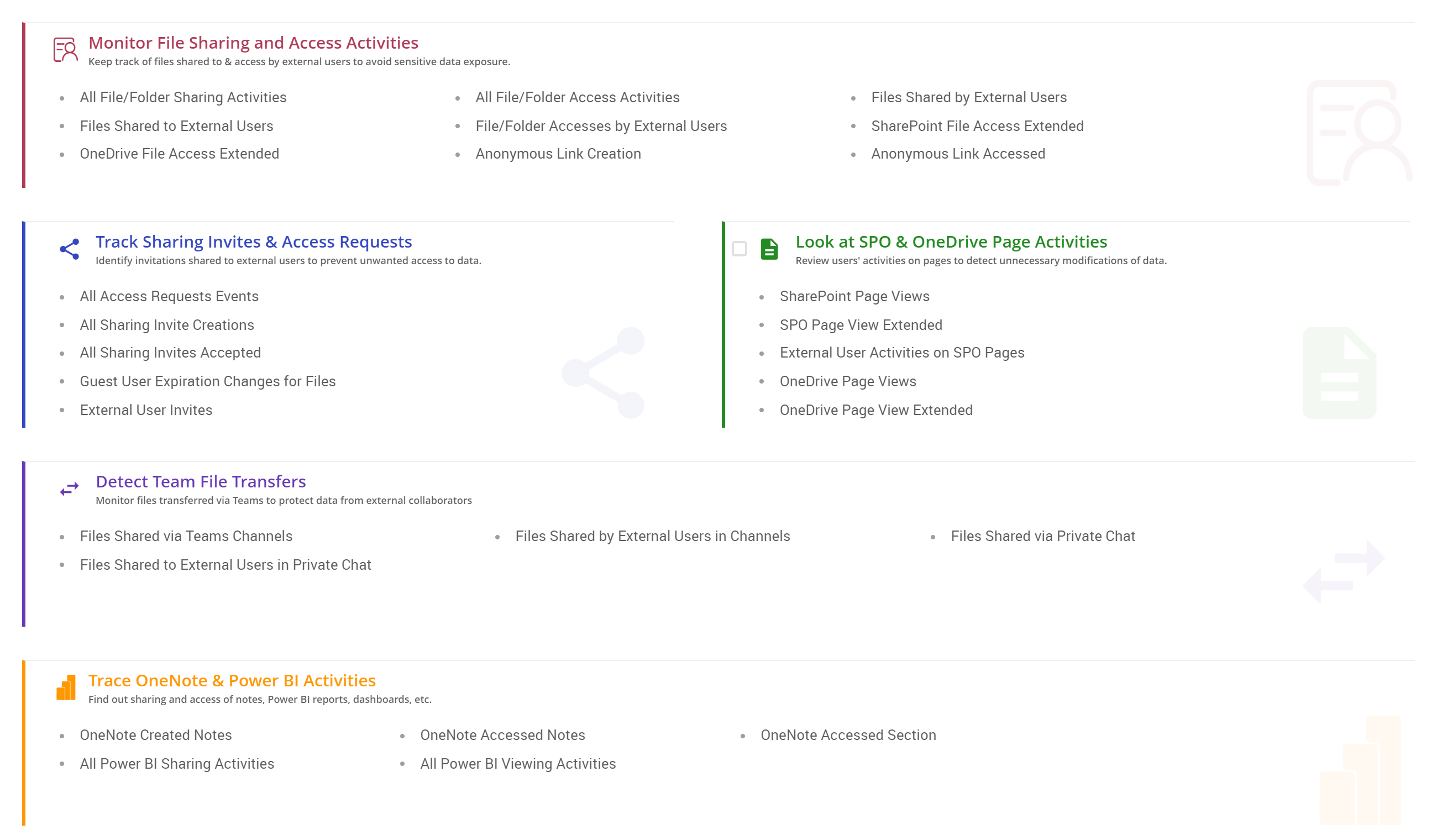
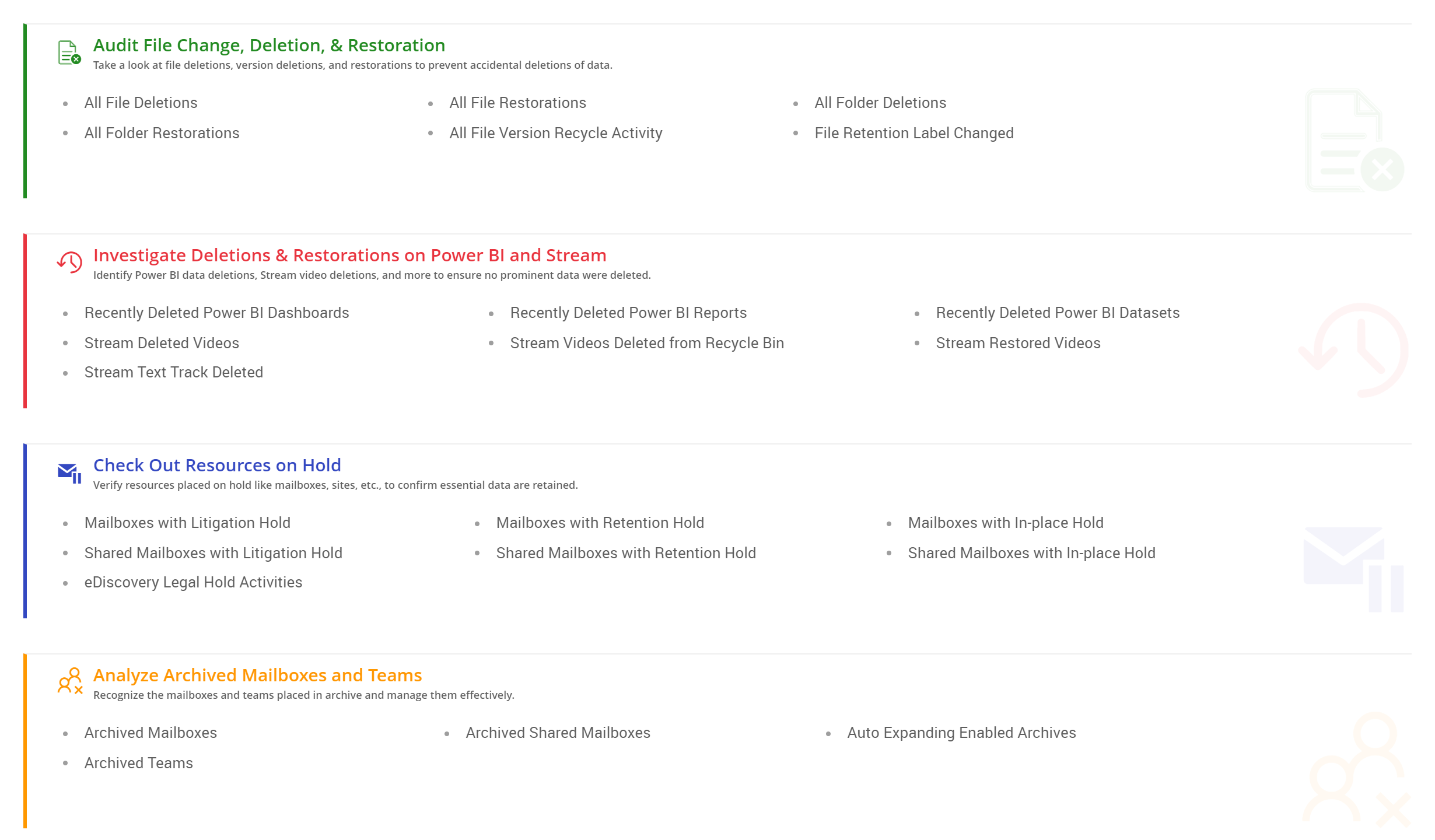
Spot file sharing & access and identify data deletions & recovery activities instantly.
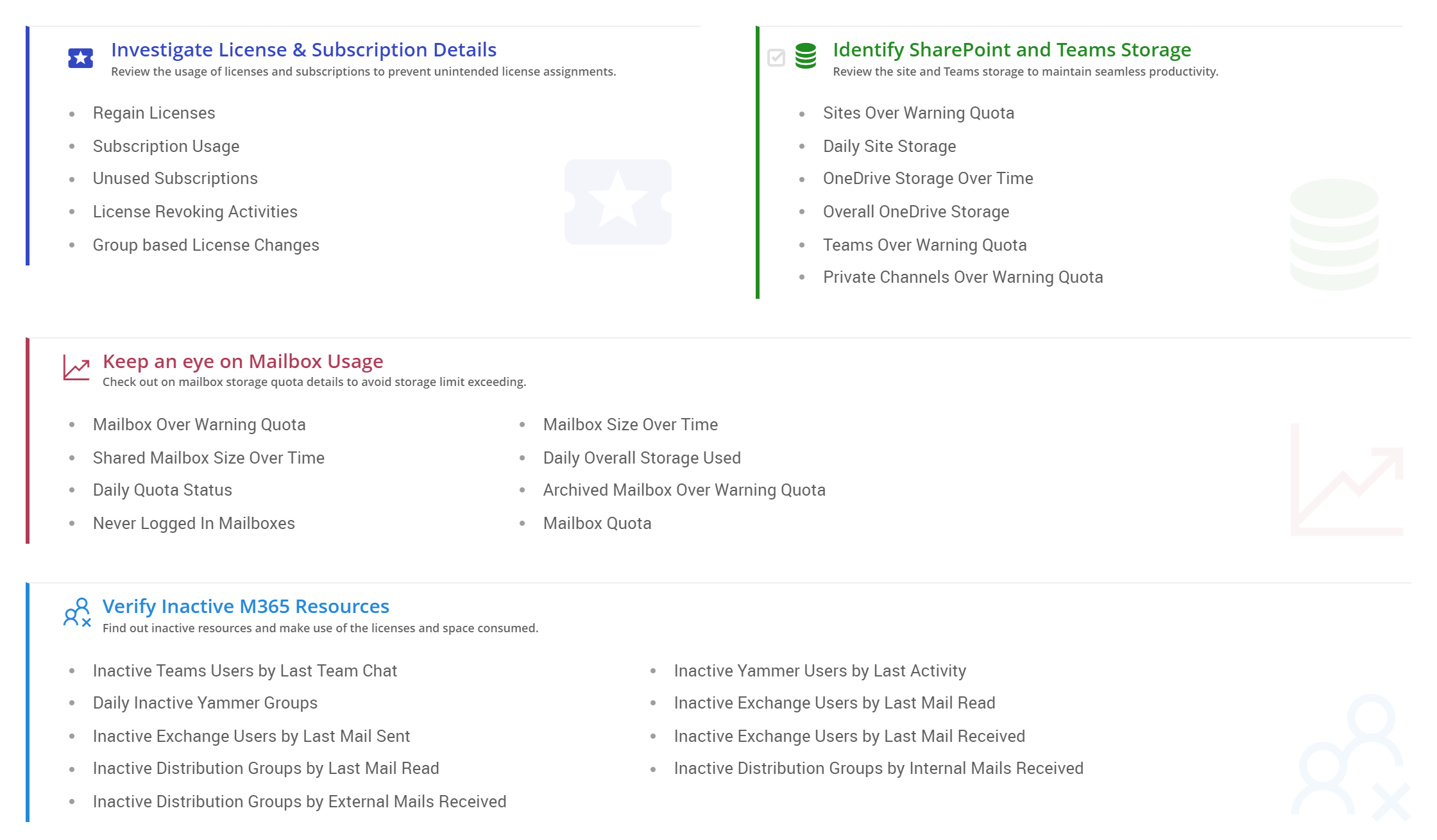
Keep track of resource usage and find inactive resources.
Verify user identity and review configured authentication details.
Monitor user roles and access privileges in various services.
Discover risky sign-ins, threat protection stats, and risk-resolved details to improve data security.
Report Board for ISO:27001
AdminDroid offers a dedicated Report Board curated for the centralized management of ISO reports.
Benefits of Choosing AdminDroid for your ISO:27001 Compliance

Maintain an up-to-date list of security policy implementations and changes
- ISO:27001 audit requires you to secure the information systems in the organization from various threats.
- AdminDroid provides you with details on configured security policies and any crucial changes made to critical security configurations.

Detect suspicious sharing and access of sensitive files
- Identifying suspicious file sharing with external users and sensitive files being accessed by anonymous users can prevent confidential data exposure.
- With AdminDroid, you can monitor file sharing and access details, file views, and page views across all Microsoft 365 services.

Spot accidental deletions of critical data and ensure successful recovery
- Managing information systems requires retaining critical data and avoiding unwanted or accidental deletions. Also, it is prominent to recover those data before they get deleted permanently.
- AdminDroid’s wide-ranging reports help you to find file deletions from every stage of recycle bin and allow you to monitor recovered files too.

Ensure only authorized users access the information systems
- Monitoring user identities and ensuring whether strong authentication methods are implemented in your organization is significant for preventing authentication attacks.
- AdminDroid gives you in-depth details about organizational users, external users, user password details, and authentication details configured, like MFA, CA policies, etc.

Identify risky happenings and assure their timely resolution
- Finding out risky sign-ins, suspicious sign-in attempts, and email threat detections are prominent for preventing data loss. In addition, you must verify that all the critical risks are resolved properly.
- Utilizing AdminDroid, you can get cutting-edge details with appealing graphs for all the risky activities and risk-resolved details in your organization. Also, you will be notified at the right time to mitigate risks effectively.